Network management is the process of monitoring, configuring, securing, and optimizing network infrastructure to ensure reliable, high-performance connectivity across an organization. It brings together core functions such as network monitoring, fault and configuration management, performance management, security controls, traffic analysis, provisioning, and inventory tracking, often organized under the FCAPS framework. These components work collectively to maintain stability, visibility, and control across complex network environments.
Modern network management is enabled by Network Management Systems (NMS) that provide centralized visibility, automation, and scalability across on-premises, cloud, and hybrid infrastructures. By leveraging real-time analytics and automated workflows, organizations can reduce downtime, strengthen security, control operational costs, and scale networks efficiently. As a result, network management supports consistent digital service delivery and aligns network operations with evolving business demands.
What Are the Key Components of Network Management?
The key components of network management include network monitoring, fault management, configuration management, performance management, security management, and traffic analysis. These functions are commonly organized under the FCAPS model (Fault, Configuration, Accounting, Performance, and Security), which provides a standardized framework for managing network operations. These features work together to help organizations maintain network reliability, strengthen operational control, and deliver consistent services across their network infrastructure.
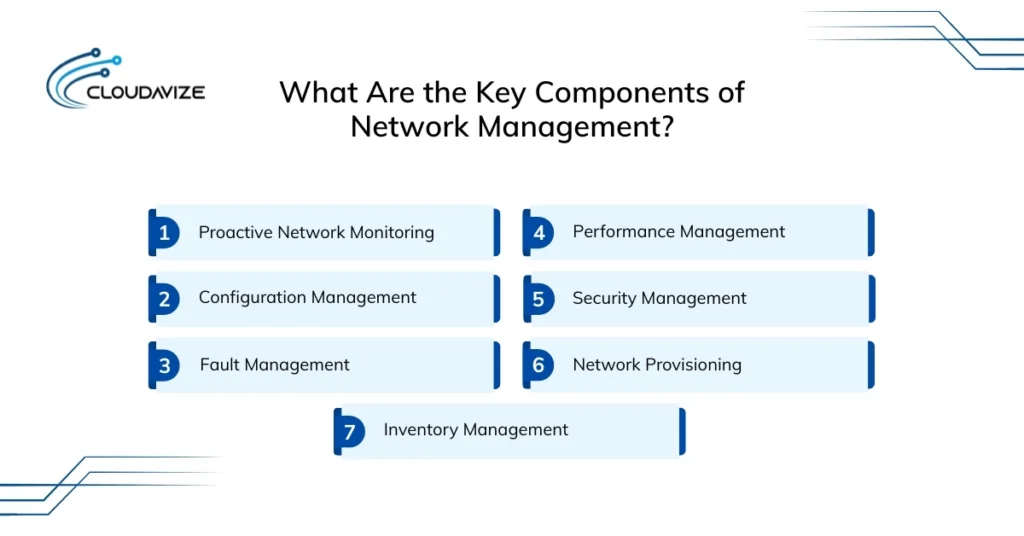
7 key components of network management are:
- Proactive Network Monitoring
Under network monitoring, the overall health of the network, including traffic behavior and topology structure, is continuously observed by tracking the status of devices such as routers, switches, and firewalls. Management software supports this process by using protocols such as SNMP (Simple Network Management Protocol) and ICMP to poll devices for uptime, performance metrics, and real-time health metrics. This continuous visibility enables early detection of hardware issues, allowing IT teams to replace or remediate failing components before localized outages occur. - Configuration Management
Configuration management tracks, controls, and updates the configuration of network devices across the infrastructure, using centralized network management systems. It defines configuration baselines, records changes, enforces compliance policies, and enables rapid rollback in the event of errors. This approach reduces human error, maintains consistency across multi-vendor environments, and lowers operational risk. For businesses, including SMBs, it simplifies network administration and supports scalable infrastructure growth. - Fault Management
One of the core features of network management is fault management, which identifies, isolates, and resolves network issues that disrupt operations through real-time monitoring and alerting. It detects device failures, link outages, and service degradation, enabling network teams to analyze root causes and implement corrective actions, such as restarting services or rerouting traffic. This capability reduces downtime, speeds up issue resolution, and improves overall network availability for business-critical systems. - Performance Management
Performance management measures how efficiently the network delivers data and services by collecting metrics such as throughput, response time, jitter, and utilization across network segments. By analyzing these metrics, organizations can identify congestion points, optimize traffic flow, and align network resources with application requirements. This feature supports consistent service delivery, improves application performance and user experience, and ensures the network can meet business demand during peak usage periods. - Security Management
This network management feature protects infrastructure from unauthorized access, data breaches, and cyber threats by managing firewalls, VPNs, and Intrusion Detection Systems (IDS), and enforcing strict access control lists (ACLs). Security management systems analyze traffic patterns to detect anomalies and enforce security rules across devices and network segments. The business impact includes reduced exposure to security incidents, improved regulatory compliance, and stronger protection of sensitive organizational data. - Network Provisioning
Network provisioning manages the deployment and activation of network resources and services by allocating IP addresses, configuring devices, and enabling connectivity for users, applications, and locations. Automation accelerates provisioning processes by reducing manual intervention and standardizing deployment workflows. For businesses, effective network provisioning enables faster onboarding, supports expansion initiatives, and ensures the network adapts efficiently to changing operational requirements. - Inventory Management
Inventory management tracks all network devices, components, and software assets within the network infrastructure by maintaining an up-to-date inventory database that records device types, locations, configurations, and lifecycle status. Accurate inventory management supports maintenance planning, compliance audits, and capacity forecasting while reducing asset-related risks. For businesses, it improves operational visibility and ensures effective utilization of network resources.
What Are the Core Capabilities of Network Management Systems?
Core capabilities of Network Management Systems (NMS) include end-to-end network visibility, threat detection, automation, and scalability, which together ensure that network infrastructure supports business operations without disruption. These capabilities provide centralized, real-time insight into network devices and services, enabling organizations to maintain smooth, reliable, and controlled network operations across complex environments.
Here are the 8 core capabilities of network management systems:
- End-to-End Network Visibility
End-to-end network visibility refers to the ability to view the entire network environment, including devices, traffic flows, and performance metrics, from a centralized interface. It aggregates data from routers, switches, access points, and monitoring tools into a unified dashboard. The end result is complete operational awareness, enabling faster troubleshooting, improved decision-making, and consistent network performance across all segments. - Proactive Threat Detection
One of the major capabilities of NMS is proactive threat detection, which enables immediate identification, logging, and alerting of network issues or outages, reducing mean time to repair (MTTR). Modern NMS, especially those that use AI and ML, function as centralized command centers that continuously analyze network behavior to sustain uptime. By applying behavioral anomaly detection and hypothesis-driven investigations, these systems uncover Indicators of Compromise (IOCs) and attacker tactics that bypass perimeter defenses, strengthening overall security posture. - Cross-Platform Device Support
Cross-platform device support is a foundational requirement for modern Network Management Systems (NMS), enabling IT teams to monitor, manage, and secure diverse, multi-vendor, and multi-OS environments from a single, centralized console. It is performed using standardized communication protocols such as SNMP, SSH, and APIs to translate different vendor languages into a common management format. With this step, the end result is simplified network administration, reduced compatibility issues, and consistent control across diverse network infrastructures. - Automated Workflow Management
With NMS, routine network tasks such as configuration updates, traffic rerouting, and policy enforcement are executed automatically through automated workflow management. This capability relies on predefined rules, scripts, and automation engines built into the network management system. For example, traffic can be automatically rerouted to a secondary path when a primary link reaches 90% capacity. The result is faster operational execution and the elimination of manual configuration errors that often cause network instability. - Real-Time Performance Analytics
In NMS, real-time performance analytics continuously processes live network data to deliver immediate, actionable insights into network speed, health, and overall usage. This capability streams telemetry data to analytics engines that calculate critical metrics such as latency, jitter, and packet loss within milliseconds. This continuous visibility enables the IT team to make data-driven decisions in real time and maintain high service levels for all end users. - Scalable Infrastructure Operations
Scalable infrastructure operations refer to a network system design that allows the management layer to grow seamlessly alongside the physical network without any loss in performance. This is typically achieved through a modular or cloud-native architecture that can dynamically add pollers or increased processing power as new branch offices and devices are integrated. Ultimately, this future-proofs the business by ensuring that rapid network infrastructure expansion never crashes the underlying management framework. - Remote Access and Control
With remote access and control capabilities, network administrators can securely configure, manage, and troubleshoot network devices from any location in the world. By using encrypted tunnels, such as VPNs or Secure Shell (SSH), IT staff can gain deep-level access to the command-line interface (CLI) of remote hardware just as if they were physically present. This capability significantly reduces the need for expensive on-site truck rolls, saving the organization, especially SMBs, substantial travel time and operational expenses. - Intelligent Anomaly Identification
Unusual network behavior is identified through intelligent anomaly identification, which analyzes historical and real-time data to detect deviations from established performance or traffic patterns. This analytical approach uncovers hidden issues that may not trigger standard alerts and typically learns the network’s baseline behavior over several weeks, flagging only activities that deviate significantly from it. The end result is earlier issue detection, improved network stability, and reduced risk of unexpected outages.
What Are the Different Types of Network Management?
Different types of network management include centralized, distributed, cloud-based, on-premises, and hybrid. Each type follows a distinct operational approach based on deployment model, control distribution, and scalability requirements. Therefore, understanding the different network management types and selecting the right model depends on network size, geographic spread, security needs, and the degree of alignment between network operations and business applications.
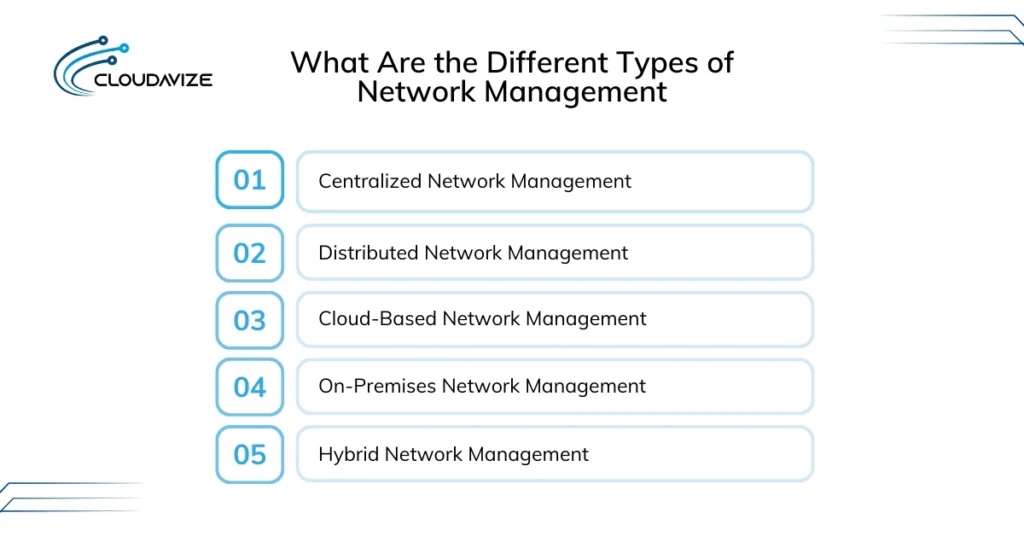
5 different types of network management are:
- Centralized Network Management
Centralized network management is a network management model in which the entire network is controlled and monitored from a single platform or unified console (cloud or on-premises). This approach involves consolidating visibility, policy enforcement, and reporting into a unified management system. Its impact includes simplified administration, consistent configuration standards, and faster troubleshooting, making it suitable for organizations with relatively contained or moderately sized networks. - Distributed Network Management
Within distributed network management, network services, management, monitoring, and control tasks are distributed across multiple systems or locations rather than relying on a single control point. This approach is implemented by deploying management software across branch offices or geographic regions, enabling local systems to independently manage traffic, faults, and performance. By reducing centralized bottlenecks and leveraging localized management agents, it improves scalability, enhances performance, and increases reliability, ensuring continued operations even if one node becomes unavailable. - Cloud-Based Network Management
Cloud-based network management delivers monitoring and control capabilities through cloud-hosted platforms accessed over the internet. It involves using a Software-as-a-Service (SaaS) platform to monitor and configure devices regardless of their physical location. This impacts the business by providing flexible scaling, rapid deployment, and lower upfront hardware costs, allowing IT teams to manage the network from any device with an internet connection. - On-Premises Network Management
Unlike cloud-based systems, which operate via an internet connection, on-premises network management requires the management system to be installed on physical hardware located within the organization’s data center. This approach involves direct control over network data, configurations, and security policies without external dependencies. Its impact includes greater control, predictable performance, and support for compliance in environments with strict regulatory or data-residency requirements. - Hybrid Network Management
Hybrid network management combines on-premises and cloud-based management models to support complex or transitional environments. It involves managing some network components locally while leveraging cloud platforms for visibility, analytics, or remote access. The result is operational flexibility, balanced control, and the ability to scale or modernize network management without full infrastructure replacement.
What Are the Benefits of Network Management for Businesses?
Network management delivers significant benefits for businesses, including reduced downtime, improved network performance, lower IT operational costs, stronger security, faster problem detection, and support for scalable growth. For small and medium-sized businesses (SMBs), these benefits are especially valuable, as they help maintain stable operations with limited IT resources. Collectively, effective network management strengthens business continuity, improves employee productivity, and ensures consistent delivery of digital services.
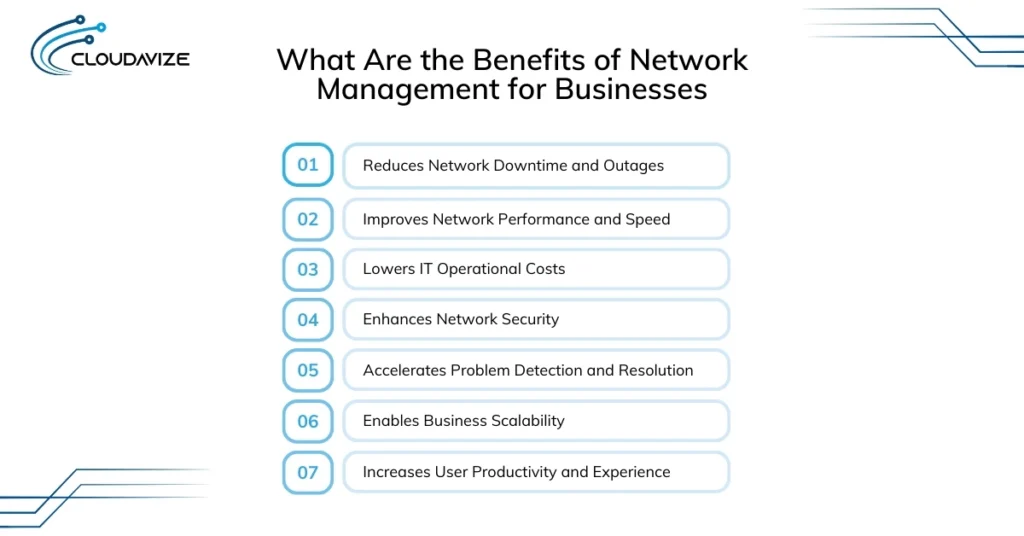
Key benefits of network management for business include:
- Reduces Network Downtime and Outages
By continuously monitoring devices and network paths, network management helps systems identify issues such as software glitches before they escalate into failures, reducing downtime. It ensures business continuity, preventing the massive revenue losses and reputational damage that occur when customer-facing services or internal databases go offline. - Improves Network Performance and Speed
Network management analyzes traffic patterns and performance metrics, helping administrators to eliminate bottlenecks and optimize data routing. This leads to faster data transmission and more reliable application performance. The impact is smoother business operations, better application responsiveness, and improved support for high-demand workloads. - Lowers IT Operational Costs
By outsourcing network management to Managed Service Providers (MSPs), businesses can significantly reduce IT operational costs by automating routine network tasks, implementing proactive monitoring, and adopting standardized processes. This approach eliminates the need for large, full-time in-house IT teams, resulting in lower staffing costs, more predictable IT spending, and a more efficient use of technology budgets. - Enhances Network Security
Network management improves security by centralizing policy enforcement, firewall controls, and real-time monitoring to detect unauthorized access or unusual data activity. It enables faster threat detection and containment. The impact is a stronger security perimeter that protects sensitive data, supports regulatory compliance, and reduces the risk of costly breaches or legal penalties. - Accelerates Problem Detection and Resolution
With real-time alerts and diagnostic tools, network management enables faster identification and resolution of network issues. Problems are detected early and addressed before users are affected which reduces MTTR, fewer disruptions, and improved reliability of business services. - Enables Business Scalability
Network management enables business scalability by using standardized configuration templates and automated provisioning to quickly add new devices, users, or branch offices. This flexibility allows organizations to expand operations and respond to new market opportunities without being constrained by rigid or poorly organized IT infrastructure. - Increases User Productivity and Experience
With network management ensuring applications remain available and perform consistently, employees avoid disruptions caused by slow connections or system errors. Reliable network performance improves employee efficiency and morale, while customers experience seamless digital interactions that increase satisfaction and strengthen long-term brand loyalty.
What Are the Common Challenges in Network Management?
Common challenges in network management include complex environments, scalability limitations, rising security threats, and shortages of skilled IT personnel. As networks grow and become more interconnected, these challenges can result in downtime, performance degradation, increased security risk, and reduced operational agility. Effectively addressing these issues requires the right combination of tools, standardized processes, and technical expertise to maintain stable and reliable network operations.
4 common challenges in network management are:
- Complex Multi-Vendor Environments:
Complex multi-vendor environments arise when a network includes devices, software, and platforms from different manufacturers, each with its own standards and management interfaces. This occurs as organizations expand, merge, or adopt best-of-breed solutions over time. To solve this, organizations should implement a vendor-agnostic network systems, that supports standard protocols like SNMP and NETCONF, allowing all diverse devices to be managed through a unified platform. - Network Scalability Issues:
As business demands increase, network scalability issues surface when network management infrastructure cannot efficiently support growth in users, devices, applications, or traffic volumes. These challenges typically stem from rigid network architectures, manual configuration processes, or insufficient capacity planning. Organizations can address network scalability limitations by adopting modular designs, implementing automation, and using proactive capacity monitoring to align network growth with evolving business needs. - Rising Security Threats
Modern network environments face continuous, increasingly sophisticated cyber threats, including ransomware, distributed denial-of-service (DDoS) attacks, and unauthorized data exfiltration exploiting network vulnerabilities. The expansion of IoT devices and remote work further increases the attack surface, creating more entry points for exploitation through unpatched software or weak configurations. To mitigate these risks, businesses should implement a Zero Trust security framework, automate regular firmware and software patching, and use AI-driven monitoring tools. - IT Skills Shortage
The IT skills shortage reflects a growing gap between the advanced expertise required to manage modern, software-defined networks and the availability of qualified professionals. This challenge arises as rapid advancements in automation, virtualization, and cloud integration outpace traditional training and education programs. Organizations can bridge this gap by adopting network automation and AIOps tools to handle routine tasks, while investing in continuous training and certification programs such as CCNP or CompTIA Network+ for existing staff.
What Are the Best Network Management Tools and Software?
The best network management tools and software include SolarWinds Network Performance Monitor, Cisco Prime Infrastructure, PRTG Network Monitor, Nagios, and ManageEngine OpManager. These tools provide centralized visibility, monitoring, and control across network infrastructure, enabling organizations to maintain consistent performance, strengthen security, and ensure reliable network operations as environments grow more complex.
8 best network management tools and software:
- SolarWinds Network Performance Monitor
As an enterprise-focused network monitoring tool, SolarWinds Network Performance Monitor delivers deep visibility into network performance and availability by continuously collecting and analyzing device-level and traffic data. Using protocols such as SNMP, it monitors bandwidth usage, latency, packet loss, and device health. Real-time alerts and detailed performance insights support faster troubleshooting, proactive optimization, and reduced network downtime. - Cisco Prime Infrastructure
Cisco Prime Infrastructure (PI) is a comprehensive network management platform offering centralized lifecycle management for wired and wireless campus and brand networks. This platform integrates monitoring, configuration management, and lifecycle management for wired and wireless networks. By providing unified visibility and policy enforcement, it helps organizations simplify network operations, maintain configuration consistency, and improve overall network reliability. - PRTG Network Monitor
Paessler PRTG Network Monitor is an all-in-one, flexible monitoring solution that tracks network performance, availability, and traffic via sensor-based monitoring. It uses protocols such as SNMP, WMI, and SSH to continuously collect metrics from network devices, applications, and services. By providing customizable alerts and clear performance dashboards, PRTG helps organizations quickly identify issues, simplify monitoring tasks, and resolve network problems efficiently. - Nagios
As a widely used open-source IT infrastructure monitoring platform, Nagios monitors servers, networks, and applications to maintain operational uptime. This platform provides real-time status checks, performance monitoring, and alerting through email or SMS across environments such as Windows, Linux, switches, and routers. It enables early issue detection, faster response, and reduced downtime through proactive monitoring. - ManageEngine OpManager
ManageEngine OpManager is a comprehensive and powerful network management software that combines monitoring, fault management, and performance analysis. It collects real-time data from network devices and presents it through dashboards and reports. Its contribution is improved operational visibility, faster fault resolution, and simplified management of complex network environments. - Datadog Network Monitoring
Network monitoring from Datadog provides cloud-based visibility across on-premises, cloud, and hybrid environments by analyzing network traffic and performance in real time. It operates by collecting flow data and telemetry to identify communication patterns, latency issues, and performance bottlenecks. This capability supports modern, distributed infrastructures and allows teams to correlate network behavior with application and system metrics for faster troubleshooting and informed operational decisions. - Splunk Enterprise
Splunk Enterprise is a data analytics platform that indexes and analyzes large volumes of machine-generated data across IT environments. Collecting logs from network devices such as routers, firewalls, and servers, it enables advanced searching and correlation through SPL-driven dashboards. In network management, Splunk helps uncover hidden patterns, detect anomalies, and support advanced troubleshooting across IT and security teams. - Zabbix
Zabbix is an open-source, enterprise-class monitoring platform built for real-time visibility across network infrastructure, servers, cloud services, and applications. It collects data using agent-based and agentless methods, including SNMP (v1–v3) and traps, to track bandwidth usage, traffic patterns, device health, and performance metrics. With features such as flexible alerting, auto-discovery, network mapping, and high scalability, Zabbix enables cost-effective monitoring and reliable management of networks of varying sizes.
What Are the Different Types of Network Management Protocols?
Different network management protocols such as SNMP, NetFlow, ICMP, Syslog, WMI, and SSH are standardized rules used to monitor, configure, and maintain network health and performance. These protocols enable structured communication between network devices and management systems, allowing administrators to track traffic behavior, diagnose connectivity issues, enforce configurations, and secure network infrastructure.
Here are different types of network management protocols:
- SNMP (Simple Network Management Protocol)
Widely adopted across enterprise networks, SNMP enables centralized monitoring and management of network devices such as routers, switches, servers, and firewalls by collecting information from network agents to a central management system. Network management systems use SNMP to poll devices for status and performance data or receive alerts when thresholds are breached. This standardized approach improves visibility into device health, supports proactive monitoring, and accelerates issue detection to maintain operational stability. - NetFlow
Netflow is a Cisco-developed protocol (with IPFIX being the IETF standard version) designed to collect IP network traffic, analyze, and monitor flow data. It operates by exporting metadata about network traffic from devices to a collector for analysis. The protocol helps administrators understand bandwidth usage, identify traffic patterns, and detect abnormal behavior, leading to better capacity planning, optimized performance, and improved security visibility. - ICMP (Internet Control Message Protocol)
Designed for diagnostics and error reporting, ICMP is a fundamental protocol that network devices use to exchange operational messages, such as whether a destination or service is reachable. It serves as the underlying mechanism for widely used diagnostic tools like ping and traceroute. By delivering immediate feedback on connectivity status and transit delays, ICMP enables network management systems to verify device availability and pinpoint the exact location where a connection failure occurs. - Syslog
Syslog is a standardized message-logging protocol that allows network devices and systems to send event notifications to a centralized logging server, commonly known as a Syslog server. It operates by classifying messages based on facility, which identifies the source system, and severity, ranging from emergency to debug levels. This structured logging creates a centralized and searchable audit trail of network events, enabling effective troubleshooting of intermittent issues and supporting post-incident forensic analysis and compliance requirements. - WMI (Windows Management Instrumentation)
In Windows-centric environments, WMI serves as a management framework for accessing detailed system and application-level data across Windows-based servers and workstations. Network management systems use WMI to query information such as running processes, registry configurations, resource utilization, and hardware health. It extends network management visibility into the application layer, helping ensure that servers supporting network services operate reliably and as expected. - SSH (Secure Shell)
SSH is a cryptographic network protocol used for secure remote access and command-line communication with network devices. Its primary role is to establish an encrypted tunnel between an administrator’s system and network hardware, preventing interception of credentials or configuration data. This secure channel enables IT teams to perform remote configuration changes, execute diagnostic commands, and manage geographically distributed devices without compromising network security. - RESTCONF and NETCONF
Built for programmatic network configuration, RESTCONF and NETCONF are modern protocols designed to move beyond traditional SNMP for managing devices in Software-Defined Networking (SDN) environments. They use structured data formats such as XML and JSON to communicate with network devices, making them well-suited for automation and DevOps workflows. Their adoption enables programmable infrastructure, where large numbers of devices can be configured or updated simultaneously through automated scripts with high accuracy and consistency.
What Does Network Management Services Include?
Network management services encompass managed network monitoring, network configuration, 24/7 technical support, network security, remote management, and performance optimization. These services are delivered by internal IT teams or Managed Service Providers (MSPs) to maintain consistent network availability, performance, and security. Together, they ensure stable day-to-day operations while reducing operational complexity, minimizing risk, and allowing businesses to focus on core objectives rather than network maintenance.
Key services included in network management are:
- Managed Network Monitoring
NMS offers managed network monitoring, including 24/7 surveillance of network devices, links, and traffic to detect performance issues, failures, and anomalies. It uses monitoring tools that collect real-time data on uptime, latency, bandwidth usage, and device health, triggering alerts when thresholds are exceeded. The impact is early issue detection, reduced downtime, and improved network reliability without requiring constant manual oversight. - Network Configuration Services
Network management includes complete network configuration services that handle the setup, standardization, and ongoing management of device configurations by applying predefined templates, tracking changes, and maintaining version control across routers, switches, firewalls, and access points. This approach reduces configuration errors, ensures predictable network behavior, simplifies troubleshooting, and supports scalability as the network expands. - 24/7 Technical Support
With NMS, users get 24/7 technical support including round-the-clock assistance for network-related incidents, outages, and performance issues. It works through dedicated support teams that respond to alerts, troubleshoot problems, and coordinate remediation at any time of day. The impact is faster issue resolution, minimized business disruption, and continuous operational support for critical network services. - Network Security Services
Network security services include threat monitoring, firewall management, intrusion detection, access control enforcement, and vulnerability management. These services continuously analyze network traffic, enforce security policies, and respond to suspicious activity. This service within network management helps reduce security risk, strengthen the protection of sensitive data, improve the compliance posture, and increase resilience against cyber threats. - Remote Network Management
Remote network management includes administering, monitoring, and troubleshooting network devices without on-site intervention. It works through secure remote access tools and centralized management platforms that allow administrators to manage configurations and resolve issues from any location. The impact is faster response times, reduced operational costs, and efficient management of geographically distributed networks. - Performance Optimization Services
Performance optimization services include analyzing network usage patterns and tuning configurations to improve speed, reliability, and efficiency. These services work by identifying bottlenecks, optimizing traffic flows, and aligning network resources with application requirements. The impact is improved application performance, better user experience, and a network environment that consistently supports business workloads.
What Are Common Network Management Jobs and Career Paths?
Common network management jobs include Network Administrator, Network Engineer, Network Architect, and Network Security Engineer, all focused on designing, implementing, securing, and maintaining network infrastructure. Career paths typically start with entry-level roles such as Network or Systems Administrator, where professionals develop hands-on skills in monitoring, troubleshooting, and device management. As responsibilities expand, these roles collectively form the foundation for stable, secure, and scalable network operations that support long-term business success.
Some common network management jobs and career paths are:
- Network Administrator
A network administrator manages an organization’s LAN and WAN infrastructure to ensure reliable, secure, and efficient network operations. Core responsibilities include installing and configuring routers, switches, and firewalls, monitoring network performance, troubleshooting connectivity issues, managing user access, and enforcing security controls and compliance policies. Strong knowledge of TCP/IP, DNS, DHCP, and enterprise networking hardware is essential to be a network administrator. With average salaries ranging from $81,749 to $127,209 per year, network administrator role serves as a strong entry point for building a long-term career in network management. - Network Engineer
Unlike a network administrator, a network engineer focuses on the technical design, implementation, and high-level optimization of network systems. Network engineers are responsible for building network infrastructure, configuring complex routing protocols, and ensuring both physical and virtual network components can support high traffic volumes. Their impact on the business comes from creating resilient, high-performance environments that enable bandwidth-intensive technologies such as cloud-based ERP systems and real-time video collaboration tools. Salaries typically range from $68,255 to $180,230 per year, depending on experience and specialization. - Network Operations Manager
A network operations manager oversees an organization’s network infrastructure to ensure continuous performance, security, and high availability through proactive monitoring and incident management. This role includes managing NOC teams, handling escalations, and coordinating maintenance, capacity planning, and vendor relationships. With salary ranges typically between $57,219 and $160,825 per year, the position bridges technical execution with strategic objectives, ensuring network reliability aligns with business goals and service-level commitments. - Network Security Specialist
Network security specialists play a critical role in protecting an organization’s IT infrastructure by designing, implementing, and monitoring security controls that safeguard network availability and data confidentiality. Responsibilities include managing firewalls, VPNs, and intrusion detection systems, conducting vulnerability assessments, monitoring network traffic for threats, and responding to security incidents. For this position, salary ranges typically between $64,789 and $201,838 per year, making it a high-value career option for IT professionals. - Network Architect
An IT professional who holds the position of network architect is responsible for designing and managing high-level network infrastructure, including LANs, WANs, and cloud-based systems, to ensure security, performance, scalability, and efficiency. Their role involves planning network architecture, overseeing implementations and upgrades, optimizing traffic flow, and enforcing security and compliance standards. With salary ranges typically between $95,396 and $226,865 per year, this strategic role directly supports long-term business growth, resilience, and technology alignment. - Systems Administrator
Also referred to as SysAdmins, Systems Administrators manage, configure, and maintain an organization’s IT infrastructure to ensure high availability, security, and stable operations. Their responsibilities include maintaining servers and network-enabled devices, monitoring performance, troubleshooting system and connectivity issues, and enforcing security controls across LAN, WAN, and wireless environments. In smaller organizations, they often manage routers, switches, and firewalls alongside servers, a broad scope of responsibility reflected in average salaries ranging from $55,886 to $127,209 per year, depending on experience and role complexity.
What Skills and Certifications Are Required for Network Management?
Network management demands skills in network configuration and administration, network monitoring and troubleshooting, security implementation, and performance optimization, supported by certifications such as CCNA and CCNP to validate expertise. A proper combination of skills and certification demonstrates the expertise and standardized knowledge to support secure, reliable, and scalable network operations.
Essential Skills for Network Management Professionals
A network management professional must have essential skills such as network configuration and administration, continuous monitoring and troubleshooting, protocol-level understanding, security implementation, performance optimization, and automation. These skills are critical for maintaining network reliability, preventing outages, securing infrastructure, and ensuring that network operations scale efficiently with business demands.
6 essential skills network management professionals must have are:
- Network Configuration and Administration: Involves setting up and managing routers, switches, and firewalls to ensure stable connectivity and consistent network behavior. This skill is acquired through hands-on labs, device configuration practice, and real-world network administration experience.
- Network Monitoring and Troubleshooting: Centers on continuously observing network performance and identifying issues such as outages, latency, or packet loss before they escalate. Expertise is built through the use of monitoring tools, responding to live incidents, and applying structured troubleshooting methods in production environments.
- Understanding of Network Protocols: Emphasizes working knowledge of protocols such as TCP/IP, DNS, DHCP, and SNMP that govern how devices communicate. Mastery is achieved through structured study, certification preparation, and practical application in real network scenarios.
- Network Security Implementation: Focuses on protecting infrastructure by deploying firewalls, access controls, and threat-detection mechanisms to reduce cyber risk. Capability grows through security training, hands-on configuration, and exposure to real-world security events.
- Performance Analysis and Optimization: Revolves around evaluating traffic patterns, latency, and utilization to eliminate bottlenecks and improve efficiency. Skills are strengthened through performance monitoring tools, metrics analysis, and continuous network tuning.
- Automation and Scripting Skills: Includes using scripts and automation tools to manage configurations and tasks. Proficiency develops by learning scripting languages, practicing automation in lab environments, and implementing automated workflows in operational networks.
Top Network Management Certifications Required
Every network management professional must hold certifications such as Cisco CCNA/CCNP, CompTIA Network+, and Juniper Networks Certified Associate to validate their technical expertise. These certifications demonstrate standardized knowledge, improve job readiness, and strengthen professional credibility, ensuring individuals are equipped to manage secure, reliable, and scalable network environments.
Key network management certifications every professional should have include:
- Cisco Certified Network Associate (CCNA): Validates foundational networking skills and device configuration knowledge, making it ideal for entry-level network roles.
- CompTIA Network+: Covers core networking concepts across vendors, helping IT professionals build a strong, neutral foundation.
- Cisco Certified Network Professional (CCNP): Demonstrates advanced skills in enterprise networking, routing, and troubleshooting for senior IT technical roles.
- Juniper Networks Certified Associate (JNCIA): Confirms proficiency in Juniper-based networking environments and core routing concepts.
- Certified Information Systems Security Professional (CISSP): Validates advanced security knowledge, essential for network security and leadership roles.
- VMware Certified Professional (VCP-NV): Focuses on network virtualization skills, supporting modern data center and cloud-based networks.
What Are Common Use Cases for Network Management?
Common network management use cases include connecting multi-site branch offices, ensuring regulatory compliance in healthcare and finance, supporting educational and manufacturing environments, and delivering reliable services in retail, hospitality, telecommunications, and government sectors. Across these industries, network management enables secure connectivity, consistent performance, and centralized control, helping organizations minimize risk, maintain uptime, and support mission-critical operations.
Here are the common use cases for network management across different sectors:
- Multi-Site Branch Office Connectivity
For companies with multiple-locations, network management connects branch offices through centralized monitoring, secure WAN links, and standardized configurations. This setup ensures consistent performance, simplifies troubleshooting across locations, and enables seamless communication between offices, supporting business continuity and operational efficiency. - Healthcare Network Compliance
In healthcare environments, network management supports secure connectivity between medical devices, patient systems, and clinical applications. It includes continuous monitoring, access control, and audit logging to meet regulatory requirements. The impact is reliable system availability, protected patient data, and compliance with healthcare regulations. - Financial Services Transaction Monitoring
Financial institutions use network management to monitor transaction flows, latency, and system availability across trading platforms and banking systems. This includes traffic analysis, security monitoring, and redundancy management. With implementation of network management in the financial sector, the result is faster transaction processing, reduced fraud risk, and uninterrupted financial operations. - Educational Institution Network Administration
Educational institutions rely on network management to support campuses with students, faculty, and digital learning platforms. It includes managing wired and wireless networks, access controls, and performance monitoring. The impact is stable online learning, secure access to resources, and improved user experience for academic communities. - Manufacturing Plant Operations
In manufacturing environments, network management connects production systems, sensors, and control networks. It ensures low latency, high availability, and rapid fault detection across operational technology networks. This supports uninterrupted production, minimizes downtime, and improves operational efficiency. - Retail Point-of-Sale Systems
Within retail environments, network management ensures reliable connectivity among point-of-sale terminals, inventory systems, and payment gateways by continuously monitoring and enforcing security controls. The result is faster checkout processing, an improved customer experience, and reduced revenue loss from network disruptions or payment system downtime. - Telecommunications Service Delivery
Telecommunications providers depend on network management to monitor large-scale networks, manage traffic loads, and maintain service quality. This includes fault management, performance analytics, and capacity planning. Implementing network management in telecommunications results in consistent service delivery, reduced outages, and improved customer satisfaction. - Government Agency Networks
Government agencies apply network management to secure and manage critical infrastructure across departments and locations. It includes access control, compliance monitoring, and centralized oversight. The impact is secure communication, regulatory compliance, and reliable delivery of public services. - Hospitality Guest Network Management
In the hotel and hospitality industry, they use network management to deliver secure, high-performance guest Wi-Fi while separating internal systems from guest traffic. Monitoring and bandwidth management ensure consistent service quality. This enhances guest satisfaction and protects internal business systems.
What Are Common Myths About Network Management?
Common myths about network management include the belief that it is only necessary for large enterprises, that it is too expensive, that simply adding bandwidth solves performance issues, or that modern networks can run reliably without active oversight. In reality, unmanaged or poorly managed networks are more prone to downtime, security breaches, and performance issues, especially as cloud services, remote work, and connected devices increase complexity for organizations of all sizes.
Clearing these misconceptions helps businesses recognize that effective network management is a proactive investment rather than a reactive cost. When implemented correctly, network management improves visibility, strengthens security, reduces operational disruptions, and enables networks to scale smoothly, ultimately supporting more reliable and efficient business operations.
How Has Network Management Evolved Over Time?
Network management has evolved from manual, device-by-device configuration using command-line interfaces (CLI) to intelligent, AI-driven, software-defined ecosystems. In the late 1980s and early 1990s, network management was primarily reactive and device-by-device, relying on the Simple Network Management Protocol (SNMP) to poll individual hardware for status updates.
As networks grew in size and complexity in the 2000s, centralized monitoring emerged through protocols such as SNMP, enabling basic visibility and alerting. This phase marked a shift toward policy-based, automated management, where predefined rules governed network behavior and reduced reliance on constant manual intervention.
In the modern era, software-defined networking (SDN), intent-based networking (IBN), automation, and AIOps (Artificial Intelligence for IT Operations) have transformed network management into a proactive and strategic function. Cloud computing, IoT, and hybrid infrastructures increased scale and complexity, driving the need for centralized control, end-to-end visibility, and stronger security models such as zero trust.
Today, AI and machine learning enable predictive analytics, automated remediation, and self-healing networks, allowing network management administrators to focus less on troubleshooting and more on designing resilient, scalable, and performance-optimized network architectures aligned with business intent.
What Are the Best Practices for Effective Network Management?
Best practices for effective network management include thorough documentation of network infrastructure, continuous performance monitoring, automation of repetitive tasks, implementation of strong security controls, and ongoing training for IT teams. Together, these practices improve visibility, reduce operational risk, and ensure reliable, scalable network operations.
9 best practices for effective network management:
- Document Your Network Infrastructure Thoroughly: Maintain accurate documentation of network topology, device inventories, configurations, and dependencies. This practice simplifies troubleshooting, accelerates onboarding, and reduces errors during upgrades or incident response.
- Monitor Network Performance Continuously: Use real-time monitoring tools to track uptime, latency, bandwidth usage, and device health. Continuous monitoring enables early issue detection, faster resolution, and sustained application performance.
- Automate Repetitive Management Tasks: Apply automation for repetitive tasks such as configuration updates, provisioning, backups, and alerts. Automation reduces manual effort, minimizes configuration errors, and improves operational efficiency at scale.
- Implement Strong Security Policies: Enforce access controls, firewall rules, patching schedules, and monitoring policies across the network. Strong security practices reduce exposure to cyber threats and support regulatory compliance.
- Standardize Configuration Across Devices: Use configuration templates and version control to maintain consistency across routers, switches, and firewalls. Standardization simplifies management, improves reliability, and speeds up troubleshooting.
- Plan for Network Capacity and Growth: Analyze usage trends and forecast future demand to avoid congestion and performance bottlenecks. Proactive capacity planning ensures the network can support business expansion without disruption.
- Train Your IT Team Regularly: Provide ongoing training on new technologies, tools, and security practices. A skilled IT team responds faster to incidents and adapts more easily to evolving network environments.
- Establish Clear Change Management Procedures: Define structured processes for testing, approving, and documenting network changes. Clear change management reduces outages caused by unplanned or poorly executed updates.
- Partner with Experienced Network Management Providers: Collaborating with expert network management service providers allows organizations to extend internal capabilities through 24/7 monitoring, expert guidance, and proactive support.
What Are the Future Trends in Network Management?
Future trends in network management focus on AI, intent-based networking, autonomous, AIOps, and edge computing to handle growing complexity across cloud, hybrid, and distributed environments. These advancements shift network operations from manual oversight to predictive, self-optimizing systems that improve reliability, reduce operational overhead, and align network behavior directly with business objectives.
- AI and Machine Learning-Driven Automation
Advanced AI and machine learning techniques are increasingly used to analyze network telemetry, logs, and traffic patterns to automate responses to faults and performance issues. Continuous learning enables systems to detect anomalies and trigger corrective actions without manual input. The result is faster issue resolution, reduced operational workload, and improved efficiency across network operations. - Intent-Based Networking
Rather than configuring devices individually, intent-based networking allows administrators to define high-level business outcomes, such as prioritizing collaboration traffic. These objectives are automatically translated into enforceable network policies and continuously validated against real-time conditions. This approach aligns network behavior with organizational goals and enables rapid adaptation to changes like remote work or new application rollouts. - Autonomous Self-Healing Networks
Built on automation and AI-driven decision logic, self-healing networks can detect, diagnose, and resolve failures as they occur. When disruptions such as hardware faults or link outages are identified, traffic is automatically rerouted or services are restored using redundant paths. This capability delivers high resilience, minimizes downtime, and significantly reduces mean time to repair (MTTR). - AIOps for Network Operations
AIOps for Network Operations applies artificial intelligence to network operations by unifying large volumes of observability data from logs, metrics, and traces into a single intelligent view. These platforms correlate events across the entire technology stack to quickly identify root causes, rather than overwhelming teams with isolated alerts. For businesses, AIOps reduces alert fatigue, enables predictive capacity planning, and helps prevent performance issues before they impact end users. - Edge Computing Integration
Edge Computing Integration refers to shifting data processing and network management closer to data sources, such as IoT devices, sensors, and remote branch locations, rather than relying solely on centralized cloud infrastructure. This is achieved by deploying edge gateways or localized compute nodes that process time-sensitive data locally and forward only critical insights to the core network. To businesses, this approach delivers ultra-low latency for mission-critical applications, reduces bandwidth consumption, and enables real-time operations in environments where speed and reliability are essential. - Zero Trust Security Architecture
Moving away from perimeter-based security, Zero Trust enforces continuous verification of every user and device attempting to access network resources. Identity-based controls, micro-segmentation, and device posture validation restrict access at every layer. This structure limits breach impact by preventing lateral movement and safeguarding sensitive systems even when individual components are compromised.