Network security management is the practice of planning, implementing, and protecting an organization’s network infrastructure, data, and systems through coordinated tools, policies, and procedures. Its key components include firewalls and Next-Generation Firewalls (NGFW) to filter and monitor traffic, intrusion detection and prevention systems (IDPS) to identify and block threats in real time, and SIEM platforms for centralized log collection and analysis.
It functions by deploying these tools, configuring access controls and security policies, continuously monitoring network activity, analyzing threats, executing incident response procedures, and updating security controls based on findings. Clear policies such as access control, data encryption, incident response, acceptable use, and remote access help mitigate risk, maintain compliance, and ensure a resilient network environment.
Effective network security management protects against cyber threats, prevents unauthorized access, ensures regulatory compliance, provides centralized control, accelerates threat detection, reduces downtime, and optimizes security costs. Conversely, poor management can result in data breaches, malware attacks, operational disruptions, regulatory penalties, and reputational damage.
What Are the Key Components of Network Security Management?
Key components of network security management are firewalls, intrusion detection/prevention systems, security information and event management (SIEM), network access control, and identity management. Each component performs a specific function within the broader security and management framework to create centralized management, continuous monitoring, and controlled access across enterprise network security environments.
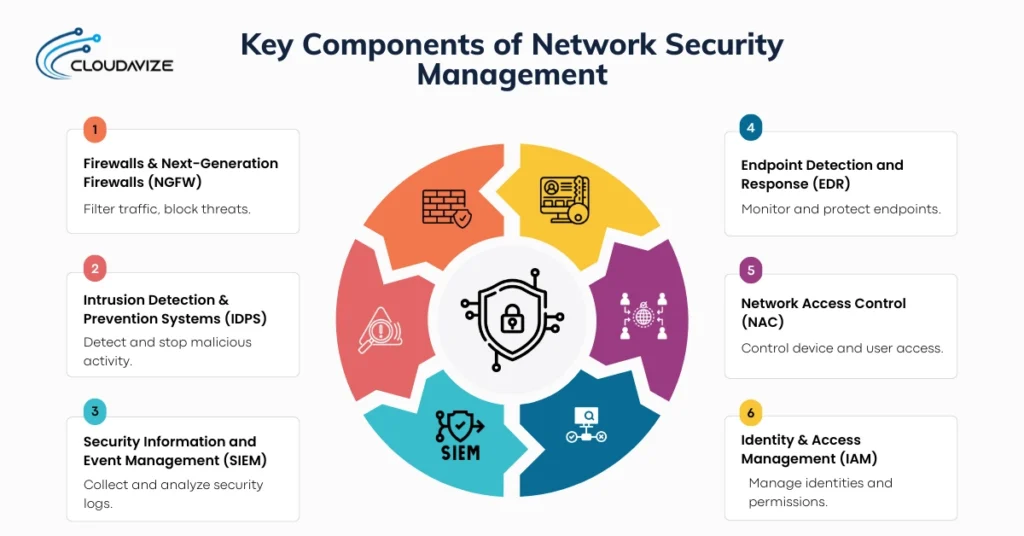
6 key components of network security management are:
- Firewalls & Next-Generation Firewalls (NGFW)
Acting as the first line of defense in network management security, firewalls monitor and filter incoming and outgoing network traffic based on predefined security policies to stop threats before they reach critical systems. While traditional firewalls filter traffic based on ports and protocols, Next-Generation Firewalls (NGFW) go deeper by integrating intrusion detection, application awareness, and deep packet inspection within a centralized firewall management system. These components of network security management form a robust framework that prevents unauthorized access and reduces exposure to cyber threats such as SQL injection and malware, ensuring secure, filtered communication. - Intrusion Detection & Prevention Systems (IDPS)
As a critical component of network security management, an IDS/IPS monitors network traffic for signs of suspicious activity or known attack patterns. An IDS alerts security teams to potential threats, while an IPS takes immediate action to block them in real time. By analyzing packet headers and payloads, IDPS identifies malicious behavior such as brute-force attacks, protocol violations, or abnormal traffic patterns. As part of a coordinated network security framework, IDPS enables organizations to neutralize exploits as they occur, prevent service disruptions, and maintain the operational integrity of critical systems. - Security Information and Event Management (SIEM)
Security Information and Event Management (SIEM) is a vital component of network security management platforms that collect, aggregate, and analyze security logs from firewalls, endpoints, servers, and applications. SIEM systems provide centralized visibility by correlating events across the network to detect complex or coordinated threats. This capability is crucial because dispersed logs alone cannot reveal patterns of suspicious activity. Platforms like Splunk and Exabeam enable security teams to monitor real-time network activity, generate alerts, and support structured incident response plans. By centralizing monitoring and analysis, SIEM helps organizations detect threats faster, maintain regulatory compliance, and preserve the integrity of their network infrastructure. - Endpoint Detection and Response (EDR)
In network security management, Endpoint Detection and Response (EDR) tools monitor endpoints such as laptops, servers, and mobile devices for suspicious activity. EDR systems collect telemetry data from endpoints, analyze behaviors, and automatically respond to detected threats. This is critical because endpoints often serve as entry points for malware or ransomware. EDR tools enable security teams to isolate infected devices, investigate security events, and prevent lateral movement across the network. By proactively protecting endpoints, EDR reduces the spread of threats, safeguards sensitive data, and supports overall network security posture. - Network Access Control (NAC)
Network Access Control (NAC) serves as a component of network security management that regulates which devices and users can access network resources. NAC solutions authenticate devices, verify compliance with security policies, and enforce role-based access control before granting connectivity. This is essential because unauthorized or non-compliant devices can introduce vulnerabilities into the network. By implementing NAC, organizations prevent unauthorized access, segment network traffic, and strengthen centralized security management, ensuring that only trusted devices can interact with critical systems. - Identity & Access Management (IAM)
Responsible for managing digital identities and controlling user access across systems and applications, Identity and Access Management (IAM) enforces authentication mechanisms such as multi-factor authentication and applies role-based access controls. This is vital because controlling who can access what reduces the risk of credential misuse and insider threats. IAM ensures that only authorized personnel can access sensitive data and critical resources, thereby maintaining confidentiality, supporting compliance, and enhancing the network’s overall security posture.
How Does Network Security Management Work?

Network security management involves deploying security tools, configuring access controls, monitoring network activity, detecting security threats, and executing incident response. By implementing these measures, organizations maintain continuous monitoring, ensure rapid threat detection, and adapt security controls to evolving risks, keeping critical systems and sensitive data protected.
Here is how network security management works:
- Deploy security tools across network infrastructure
The first step is to deploy network security management tools such as firewalls, intrusion detection/prevention systems, SIEM platforms, EDR solutions, NAC, and IAM across the network infrastructure. This includes installing and configuring hardware and software at critical points such as data centers, cloud environments, endpoints, and network gateways. Deploying these tools establishes a foundation for centralized management and continuous monitoring. Once tools are in place, the next step is to configure access controls and security policies to govern how network resources are accessed and used. - Configure access controls and security policies
In this step, organizations define and implement access control rules and security policies that determine who can access what resources and under which conditions. It includes role-based access control, multi-factor authentication, firewall rules, network segmentation, and compliance guidelines. Proper policy configuration ensures that only authorized users and compliant devices interact with sensitive systems. Once policies are enforced, the workflow shifts to real-time monitoring of network activity. - Monitor network activity in real-time
Continuous monitoring tracks network traffic, user activity, and system behavior to identify anomalies or suspicious patterns. This step leverages SIEM platforms, EDR telemetry, and NAC reports to maintain visibility across the entire network. Real-time monitoring allows security teams to detect emerging threats quickly and provides the data needed for in-depth analysis. Once activity is monitored, detected threats are analyzed to determine their impact and remediation steps. - Detect and analyze security threats
Security teams use collected logs, alerts, and analytics to detect potential threats such as malware, ransomware, brute-force attacks, or unauthorized access attempts. Threat analysis evaluates severity, scope, and potential impact, often using correlation from SIEM and EDR data. This step enables informed decisions for containment and mitigation. After threats are analyzed, organizations execute incident response procedures to neutralize active risks. - Execute incident response procedures
Incident response involves taking immediate action to contain and mitigate identified threats. This may include isolating compromised devices, blocking malicious traffic, patching vulnerabilities, or activating recovery protocols. The goal is to minimize disruption, prevent lateral movement, and protect sensitive data. Following the incident response, findings are reviewed to improve security controls in the next step. - Update security controls based on findings
The final step closes the loop by applying lessons learned from monitoring and incident response. Security controls, policies, and configurations are updated to address vulnerabilities, strengthen defenses, and adapt to evolving threats. This step ensures continuous improvement, maintains the effectiveness of network security management, and enables proactive protection for future operations.
What Are Key Network Security Management Policies?
Key network security management policies include access control, data encryption, incident response, acceptable use, and remote access. By establishing clear rules, responsibilities, and procedures, these policies help mitigate risks from internal and external cyber threats while ensuring compliance with regulatory standards such as GDPR and HIPAA. Together, they form the foundation of a secure, resilient, and well-managed network environment.
5 key network security management policies are:
- Access Control Policy
The access control policy implements the Principle of Least Privilege (PoLP) by defining who can access specific network resources and enforcing role-based access control (RBAC) and multi-factor authentication (MFA), ensuring that permissions are granted only as needed. To maintain this principle, security teams and HR strictly enforce the policy to prevent privilege creep, where users accumulate unnecessary access over time. By applying these controls, businesses, including SMBs, reduce the risk of unauthorized access and internal breaches, limiting lateral movement if a single account is compromised. - Data Encryption Policy
A data encryption policy protects sensitive information during storage and transmission by specifying encryption standards and key management practices across the network. It achieves this by using protocols such as AES for data at rest and TLS for data in transit, ensuring only authorized users with proper decryption keys can access the information. Implementing this network security management policy helps businesses to prevent interception, eavesdropping, and data breaches, safeguarding confidentiality and ensuring regulatory compliance. - Incident Response Policy
Outlining procedures for detecting, containing, and recovering from security breaches, along with regular, automated, or manual patching to address vulnerabilities, is a key component of network security management policy. This network security management policy clearly defines the roles, responsibilities, communication channels, and escalation steps during a cyber event. With this policy in place, businesses can ensure a structured response that minimizes downtime, reduces damage, and strengthens organizational resilience against future cyberattacks. - Acceptable Use Policy (AUP)
An Acceptable Use Policy (AUP) serves as a behavioral guide for how employees and users use network resources, helping prevent misuse and maintain security. This network security management policy clearly defines rules, responsibilities, and appropriate behavior when operating company systems and internet services. By explicitly defining what constitutes authorized use of company hardware and internet services, the AUP addresses the human risk factor in cybersecurity. - Remote Access Policy
The remote access policy is the essential governance layer for modern hybrid work, establishing secure methods for employees to connect to the network from outside the office. It mandates the use of secure technologies like Virtual Private Networks (VPNs) and Multi-Factor Authentication (MFA) to bridge the gap between home offices and the corporate core. This network security management policy extends the office’s secure perimeter to any global location, ensuring that remote access remains encrypted and does not become a vulnerable entry point for cyber threats.
What Are the Benefits of Network Security Management for Businesses?
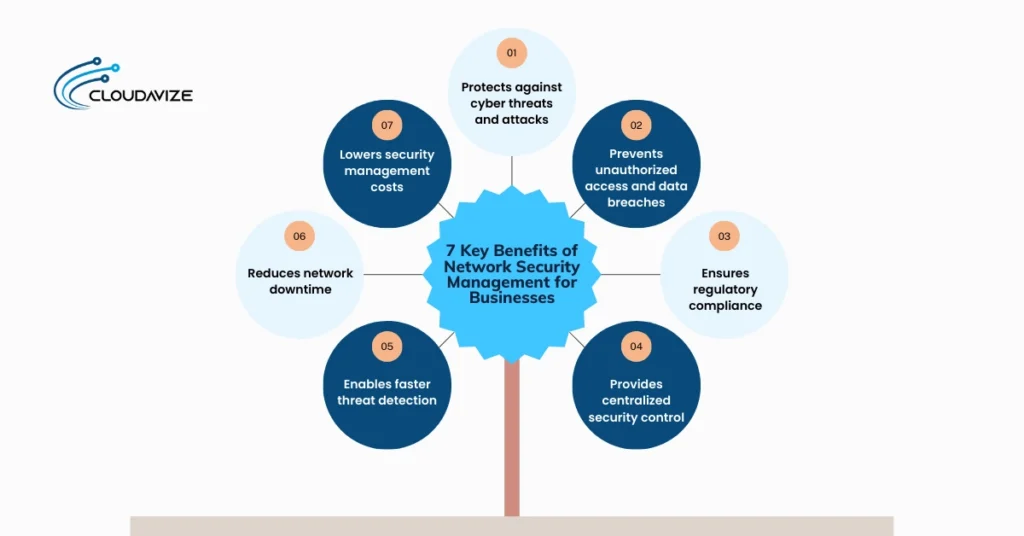
Benefits of network security management for businesses include protection against cyber threats, prevention of unauthorized access, regulatory compliance, centralized security control, faster threat detection, and reduced network downtime. These advantages help organizations maintain secure operations, safeguard sensitive data, comply with regulations, and ensure that critical systems remain available and resilient against potential disruptions.
7 key benefits of network security management are:
- Protects against cyber threats and attacks: By proactively detecting and blocking phishing, malware, ransomware, and unauthorized access, network security management shields organizations from both external hackers and internal vulnerabilities.
- Prevents unauthorized access and data breaches: By enforcing access controls, authentication, and device compliance, network security management ensures that only authorized users can access sensitive data, reducing insider threats, credential misuse, and potential breaches.
- Ensures regulatory compliance: Through structured policies, incident response plans, and centralized monitoring, network security management helps organizations meet standards such as GDPR, HIPAA, and PCI DSS, minimizing the risk of penalties and legal liabilities.
- Provides centralized security control: Centralized management by network security management consolidates monitoring, policy enforcement, and reporting across the enterprise network, giving IT teams full visibility, simplifying updates, and ensuring consistent security across all systems.
- Enables faster threat detection: Continuous monitoring with SIEM, EDR, and IDS/IPS tools allows network security management to detect anomalies and threats in real time, accelerating response and limiting potential damage.
- Reduces network downtime: By proactively identifying and mitigating threats, network security management minimizes service disruptions caused by cyber incidents. Through automated responses and continuous monitoring, network security management keeps critical systems operational, preserving business continuity and maintaining reliable network performance.
- Lowers security management costs: Effective network security management optimizes resources by automating monitoring, incident response, and policy enforcement. Centralized control reduces the need for redundant tools and manual oversight, lowering operational and staffing costs while maintaining robust protection.
What Are the Risks & Challenges of Poor Network Security Management?
The risks and challenges of poor network security management are data breaches, ransomware, malware attacks, service disruptions, regulatory penalties, and reputational damage. Without proper policies, tools, and monitoring, these challenges can escalate quickly, resulting in operational, financial, and legal consequences.
Here are the 5 major risks and challenges of poor network security management:
- Data breaches and theft: Poor network security management increases the risk of unauthorized access to sensitive customer or corporate data, including financial records, intellectual property, and confidential business information. This can lead to theft, regulatory fines, and severe financial and operational consequences.
- Ransomware and malware attacks: Weak security controls, such as unpatched systems or inadequate password policies, allow malware and ransomware to infiltrate networks. Without effective network security management, organizations struggle to detect or contain these attacks, often resulting in encrypted data, operational downtime, and potential permanent loss of critical information.
- Service disruptions: Operational downtime from cyberattacks, misconfigured firewalls, or system failures halts critical business operations. Poor network security management fails to provide proactive monitoring and mitigation, leading to increased downtime, reduced productivity, and degraded customer-facing services.
- Regulatory penalties: Failure to enforce proper security policies and conduct monitoring can result in non-compliance with regulations such as GDPR, HIPAA, and PCI DSS. Network security management lapses can lead to audits, fines, and legal liabilities, creating both financial and reputational consequences.
- Reputational damage: Security failures, publicized breaches, or service outages erode customer and stakeholder trust. Weak network security management can damage a company’s brand reputation, resulting in lost business opportunities, reduced market confidence, and long-term harm to growth prospects.
What Are the Key Network Security Management Tools?
Key network security management tools include firewalls such as Check Point and Palo Alto, network monitoring solutions like Wireshark, SIEM systems like Splunk, vulnerability scanners like Nessus, and network access tools like Gigamon. Despite falling into different group these network security management tools work together to protect networks, monitor activity, enforce policies, and manage vulnerabilities.
Below are the essential network security management tools:
Firewall and Policy Management
Working as a gatekeeper, firewall, and policy management tools such as Check Point, Palo Alto, and FireMon control network traffic, enforce security policies, and prevent unauthorized access, forming the first layer of defense in network security management.
- Check Point Software: A comprehensive firewall and security platform that integrates threat prevention, intrusion detection, and policy enforcement into one single platform. It works by filtering network traffic, monitoring suspicious activity, and applying security rules across multiple devices. For businesses, especially in sectors such as finance and government, it provides an industry-leading malware and ransomware catch rate, significantly reducing the risk of a high-profile data breach.
- Palo Alto Networks: Referred to as a global leader in network security platforms, Palo Alto Networks provides NGFW with advanced threat detection, application awareness, and centralized control. This tool inspects traffic at multiple layers, blocks malicious activity in real time, and enforces corporate security policies. By using this tool, organizations gain proactive protection against cyber threats and improved network visibility.
- FireMon: A specialized Security Policy Management (SPM) platform designed to manage the complexity of multi-vendor firewall environments. It provides real-time visibility into firewall rules and automatically flags misconfigurations and unused rules that could lead to vulnerabilities. For businesses, including large corporations and SMBs, it reduces compliance reporting time by up to 90%, ensuring they stay audit-ready for regulations such as PCI DSS and GDPR with minimal manual effort.
Network Monitoring and Intrusion Detection
Network monitoring and intrusion detection tools such as Wireshark, Snort, and Rapid7 provide the eyes of the network, which continuously observe network traffic to detect anomalies and prevent unauthorized activity, providing real-time visibility and threat alerts.
- Wireshark: Known as the world’s foremost open-source network protocol analyzer, Wireshark captures and inspects network traffic for troubleshooting and security analysis. By identifying suspicious patterns, this network monitoring tool helps security teams prevent attacks and optimize network performance.
- Snort/Suricata: As a high-performance, open-source Intrusion Detection and Prevention Systems (IDS/IPS), Suricata uses signature-based and behavioral analysis to inspect packets and employs a multi-threaded architecture for high-speed traffic handling. These tools enable organizations to block malicious traffic in real time, prevent network intrusions, and protect internal assets from lateral movement of threats.
- Rapid7 InsightIDR: A cloud-based tool that monitors endpoints, users, and network activity to detect intrusions. It integrates SIEM capabilities to provide alerts, dashboards, and response workflows, reducing dwell time for threats and improving overall security posture.
SIEM and Log Management
SIEM (Security Information and Event Management) platforms, such as Splunk and Exabeam, collect, aggregate, and analyze log data across an organization’s IT infrastructure to provide real-time visibility, detect threats, and support incident response. Integrated with tools such as EDR and firewalls, SIEM enables centralized security management, helps maintain regulatory compliance, and mitigates risks by promptly identifying and addressing suspicious activity.
- Splunk: It is a SIEM platform that aggregates log data from multiple sources, analyzes events, and provides real-time alerts. This network security management tool enables businesses to quickly detect threats, conduct investigations, and maintain regulatory compliance.
- Exabeam: Using advanced analytics and machine learning, Exabeam is a network security management tool that identifies anomalous behavior and automates threat detection. Additionally, by analyzing historical and real-time data, this network security management tool reduces manual effort and enhances response accuracy.
Vulnerability and Risk Management
Network security management tools that help to identify, assess, and prioritize security weaknesses are grouped as vulnerability and risk management tools. These tools, such as Nessus and Qualys, perform deep scans of network infrastructure to identify missing patches, misconfigurations, and outdated software versions.
- Nessus (Tenable): A vulnerability scanner that detects misconfigurations, missing patches, and security gaps across systems. Businesses use Nessus to prioritize remediation, reduce exposure, and maintain regulatory compliance.
- Qualys: A cloud-based risk and compliance platform that continuously monitors vulnerabilities across IT assets. It provides actionable reports and dashboards to help organizations proactively manage risk.
Network Access Control and Visibility
Network Access Control (NAC) and visibility tools provide real-time insights into all devices, users, and IoT/OT assets attempting to connect to the network, and enforce policies to quarantine noncompliant, unauthorized, or vulnerable endpoints. Solutions such as Gigamon and Auvik offer agentless scanning, policy enforcement, and compliance management, helping organizations maintain secure, controlled access while ensuring full visibility across their network infrastructure.
- Gigamon: It is a deep observability pipeline that provides network visibility and traffic intelligence solutions, enabling security teams to monitor, analyze, and secure network flows. This network security management tool improves threat detection, forensic analysis, and overall security efficiency.
- Auvik: A cloud-based network monitoring and management platform that maps devices, tracks performance, and enforces network policies. It enhances operational efficiency, simplifies troubleshooting, and strengthens network security posture.
What Are the Career Opportunities in Network Security Management?
Career opportunities in network security management are network security manager, network security engineer, network security analyst, and security operations center analyst. Each role focuses on different aspects of protecting an organization’s network infrastructure, monitoring threats, and ensuring compliance.
Major career opportunities in network security management include:
- Network Security Manager
A network security manager is a high-level leadership professional responsible for overseeing the overall security posture of an organization’s network. They focus on governance, budgeting, and developing security policies, bridging the gap between technical teams and executive leadership. By providing strategic direction, they help maintain secure networks, prevent breaches, and reduce cyber threats. From a salary perspective, network security managers earn between $90,023 and $158,311, depending on location, experience, and company size. Success in this role requires advanced certifications like CISSP, CISM, or Security+, along with technical expertise in firewall administration, risk management, and incident response. - Network Security Engineer
In network security engineering, professionals serve as technical specialists who design, implement, and maintain secure network infrastructure, including firewalls, VPNs, and intrusion detection systems. They configure systems, troubleshoot vulnerabilities, and ensure network resilience, helping organizations proactively prevent cyber threats and maintain reliable network performance. Salaries range from $71,942 to $180,573, and to succeed as a network security engineer, individuals need core skills in firewalls, routing/switching, and operating systems (Linux/Windows), along with certifications such as CompTIA Security+, CCNA, or CCNP Security. - Network Security Analyst
Network Security Analysts monitor network activity, analyze logs, and investigate security incidents to identify vulnerabilities before attackers can exploit them. They conduct audits, perform penetration testing, and analyze traffic using tools like Nessus and Qualys. By turning raw data into actionable intelligence, analysts enable proactive patching and defense against zero-day threats. Network security analyst salaries range from $64,357 to $209,550, with success in this role typically requiring a bachelor’s in IT or cybersecurity, hands-on experience, certifications such as CompTIA Security+, CySA+, CISSP, or CCNA - Security Operations Center (SOC) Analyst
SOC Analysts work within a Security Operations Center to detect, respond to, and mitigate security incidents in real time. Using SIEM and EDR tools, they triage alerts, investigate suspicious activity, and execute the initial steps of the organization’s incident response plan. Their constant vigilance enables faster threat detection, preventing minor security events from escalating into major breaches that could damage reputation. This role requires technical skills in network security, log analysis, and SIEM platforms, along with certifications such as CompTIA Security+ and Cisco CyberOps Associate. Salaries for SOC analysts range from $35,081 to $77,692.
Skills and Certifications Required for Network Security Management
Network security management requires a blend of technical expertise in firewalls, VPNs, and intrusion detection, coupled with certifications like CISSP, CISM, or CompTIA Security+ to validate skills and knowledge. These certifications ensure professionals can design, implement, and maintain secure network environments while helping organizations mitigate cyber risks.
Key skills and certifications required for network security management are:
- CISSP (Certified Information Systems Security Professional)
As one of the world’s most recognized certifications for experienced security professionals, the CISSP covers eight comprehensive domains of the Common Body of Knowledge, including security architecture, risk management, and incident response. To acquire this elite credential, candidates must pass a rigorous adaptive exam and demonstrate at least 5 years of cumulative, paid work experience. This certification helps professionals advance into senior leadership by providing a deep, vendor-neutral understanding of security and risk management, architecture, and engineering operations. - CISM (Certified Information Security Manager)
The CISM is a specialized certification from ISACA designed specifically for individuals looking to transition from technical execution into high-level security management. Earning the CISM requires passing a comprehensive exam and demonstrating five years of professional experience, with at least three of those years focused on management. It helps the Network Security Manager by focusing heavily on governance, program development, and incident management, aligning security practices with broader business objectives. - CompTIA Security+.
As the premier foundational certification in the cybersecurity industry, CompTIA Security+ is the essential starting point for any aspiring professional. To earn this certificate, candidates must pass the SY0-701 exam, which covers the core principles of cyber threats, attacks, and network vulnerabilities. This certification helps establish the baseline technical knowledge required for SOC Analyst and Network Security Analyst positions, ensuring a firm grasp of essential concepts such as cryptography, identity management, and secure coding. - CCNA Security (Cisco Certified Network Associate Security)
The CCNA Cybersecurity is a Cisco-specific credential that validates a professional’s ability to secure Cisco-based network infrastructure. Candidates complete Cisco-approved training and pass the certification exam to demonstrate knowledge of network security fundamentals, including secure access, VPNs, and firewall configurations. Professionals with CCNA Security skills help organizations deploy and manage secure network infrastructure effectively, strengthening overall network security management.
What Are Network Security Management Best Practices?
Best practices for network security management include centralized security policy management, regular network vulnerability assessments, network segmentation and isolation, real-time network monitoring, automated patch and update management, and well-defined incident response and recovery plans. These practices help organizations maintain a secure network environment, proactively detect and mitigate threats, ensure regulatory compliance, and minimize operational disruptions.
7 best practices for network security management are:
- Centralize security policy management across network devices
Centralizing security policy management involves consolidating policies for firewalls, access controls, and endpoints across the entire network. This can be performed using unified management consoles or security platforms that allow administrators to define, deploy, and update policies consistently. Centralization improves visibility, reduces misconfigurations, ensures consistent enforcement, and strengthens overall security posture. - Conduct regular network vulnerability assessments
Vulnerability assessments systematically scan network devices, servers, and applications to identify weaknesses, misconfigurations, or missing patches. These can be performed using automated tools such as Nessus or Qualys, combined with periodic manual reviews. Regular assessments help organizations detect risks early, prioritize remediation, and prevent potential exploits. - Implement network segmentation and isolation
Network segmentation divides the network into smaller zones based on function, sensitivity, or user access, and isolation techniques, such as VLANs or firewalls, can restrict traffic between segments. By segmenting and isolating networks, organizations contain potential threats, prevent lateral movement, and protect critical assets from widespread compromise. - Monitor network traffic in real-time
Continuous monitoring involves observing network traffic, user activity, and system events using tools like SIEM, EDR, or IDS/IPS. Real-time monitoring allows security teams to detect anomalies, identify potential intrusions, and respond proactively. This practice minimizes dwell time for threats and supports faster incident response. - Automate patch and update management
Automated patching and software updates ensure that all systems, applications, and devices remain secure against known vulnerabilities. This can be performed through centralized update servers or endpoint management tools. Automation reduces human error, accelerates vulnerability remediation, and enhances overall network security. - Develop incident response and recovery plans
Incident response plans outline procedures for detecting, containing, and recovering from security incidents. Developing these plans involves defining roles, communication protocols, escalation paths, and recovery steps. A well-structured plan minimizes downtime, limits damage, and ensures business continuity during cyber events. - Partner with trusted managed security service providers (MSSPs)
Engaging MSSPs allows organizations to leverage expert security teams, advanced monitoring tools, and threat intelligence without maintaining all resources in-house. An experienced and dedicated managed security management provider can help deploy security policies, manage incidents, and provide 24/7 oversight, enhancing protection and operational efficiency.
What Are the Future Trends in Network Security Management?
Future trends in network security management focus on zero trust architecture, AI-driven threat detection, cloud and hybrid security management, software-defined security, and automated network security operations. All of these trends are designed to enhance network protection, improve operational efficiency, and enable faster, more proactive responses to evolving cyber threats.
- Zero trust network architecture
Based on the principle of never trust, always verify, Zero Trust is a security framework that assumes no device or user is inherently trustworthy and requires continuous verification for access to network resources. By isolating network segments, Zero Trust minimizes lateral movement, ensuring that even if credentials are compromised, the rest of the infrastructure remains secure. It has evolved from static manual policies into a dynamic, AI-driven system that adjusts access levels in real time based on user behavior, device health, and geographic context. As of 2026, Zscaler has stated 81% of organizations are actively implementing Zero Trust frameworks to replace legacy VPNs and reduce the impact of breaches. - AI-driven network threat detection and response
AI-driven network threat detection and response uses artificial intelligence and machine learning to automatically identify anomalous behavior and respond rapidly to cybersecurity incidents. This approach reduces response times, improves threat prediction, and allows security teams to focus on strategic priorities rather than manual monitoring. According to Fortune Business Insights, AI-powered solutions can improve detection speed by 74% and reduce incident response times by over 50%, enabling organizations to contain threats faster, minimize potential damage, and maintain a more resilient and proactive network security posture. - Cloud and hybrid network security management
Cloud and hybrid security unify protection for data and applications across on-premises servers, private clouds, and public cloud providers such as AWS and Azure. Cloud-native security embeds protection directly into the infrastructure, offering single-pane-of-glass visibility across the network. Centralized policy management reduces misconfigurations and ensures consistent protection of sensitive data. This is critical, as Gartner predicts 99% of cloud security failures through 2026 will be due to customer errors. Cloud and hybrid security enhances visibility, compliance, and control, enabling organizations to secure multi-cloud environments efficiently and reduce operational risk. - Software-defined security and SD-WAN
Modern software-defined security and SD-WAN separate functions such as firewalls and VPNs from physical hardware, managing them entirely in software. SD-WAN is merging with security into SASE (Secure Access Service Edge), embracing identity-first networking, in which network paths are dynamically established based on verified user identity. This enables rapid deployment of secure branch offices, encrypted connectivity, and scalable network management, reducing costs and operational complexity. Organizations benefit from greater flexibility, dynamic policy enforcement, and enhanced threat isolation, making it easier to support distributed or remote workforces. - Automated network security operations
Automated network security operations use software to handle repetitive tasks such as log analysis, patch management, and initial incident triage. The trend is moving toward no-code security orchestration, enabling administrators to build complex defense workflows with drag-and-drop interfaces that run autonomously across the infrastructure. This approach reduces human error, the leading cause of security failures, minimizes network downtime, and ensures consistent protection. By automating routine operations, organizations maintain a robust security posture, accelerate incident response, and overcome challenges posed by the global cybersecurity talent shortage, thereby improving efficiency and resilience across all network environments.



